2026-01-12 19:30:25
| physical internet 8. Routing (Least-Congestion = Effective Shortest Time) and Tracking |
8. Routing (Least-Congestion = Effective Shortest Time) and
Tracking Delivery routes are computed from the destination unit's coordinates and the ledger-based map,
generating recommended routes that minimize expected delay at the current time. In physical
networks, congestion dominates delay, so the optimization principle is: 'prioritizing routes that are
less likely to clog leads to the shortest effective arrival time'.
Each unit includes an authority AI. When it detects downstream failure or congestion, it may guide a
packet to an alternate route even if it differs from the planned path. Shipment status is recorded to
the ledger as milestone events, and the app displays approximate real-time progress by reading
those events. 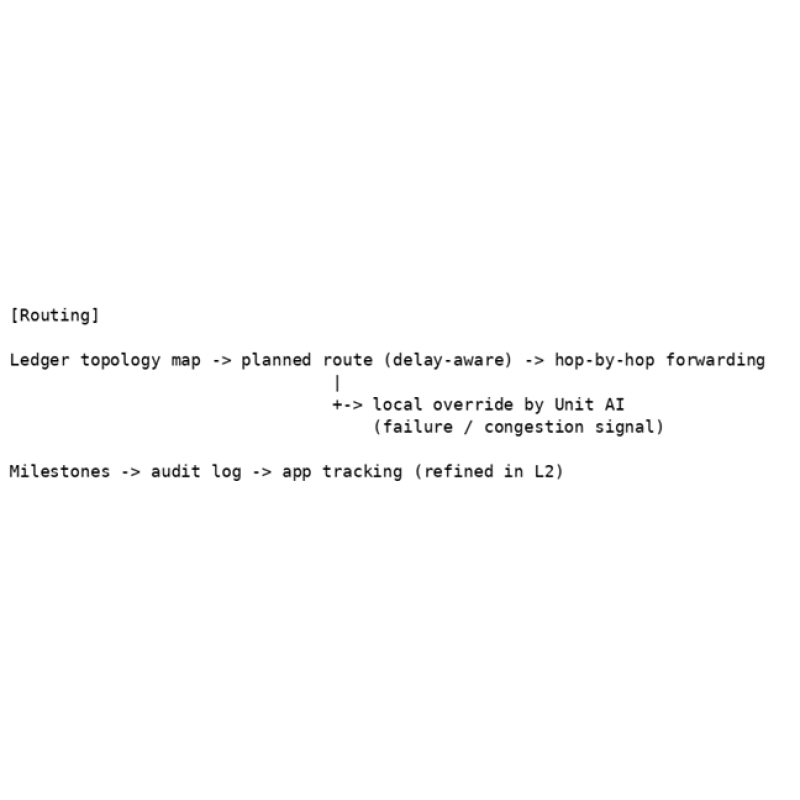
Figure 8. Routing: planned path plus local override by unit AI; milestones for tracking. |
2026-01-12 20:41:12
| physical internet 9. Tokenomics and Governance (Investment, Rewards, Usage-Based Voting) |
9. Tokenomics and Governance (Investment, Rewards,
Usage-Based Voting) To fund large construction costs, investors purchase utility-pole units similarly to real estate. Every time a
packet passes through a unit, tokens are distributed to the unit owner (each payment is small per
packet but accumulates).
For early momentum, token supply can be fixed initially; after full distribution, additional issuance may
be needed for long-term maintenance. A key feature of this proposal is voting based on usage - not
token balance. In other words, voting power is earned by using the network (sending/receiving),
rather than by holding a large balance.
To avoid fees becoming unrealistically low, maintenance operators publicly disclose electricity and
minimum operating costs and set guardrails such as a fee floor. In rural regions, a consolidated
maintenance company or local governments may install and maintain units. 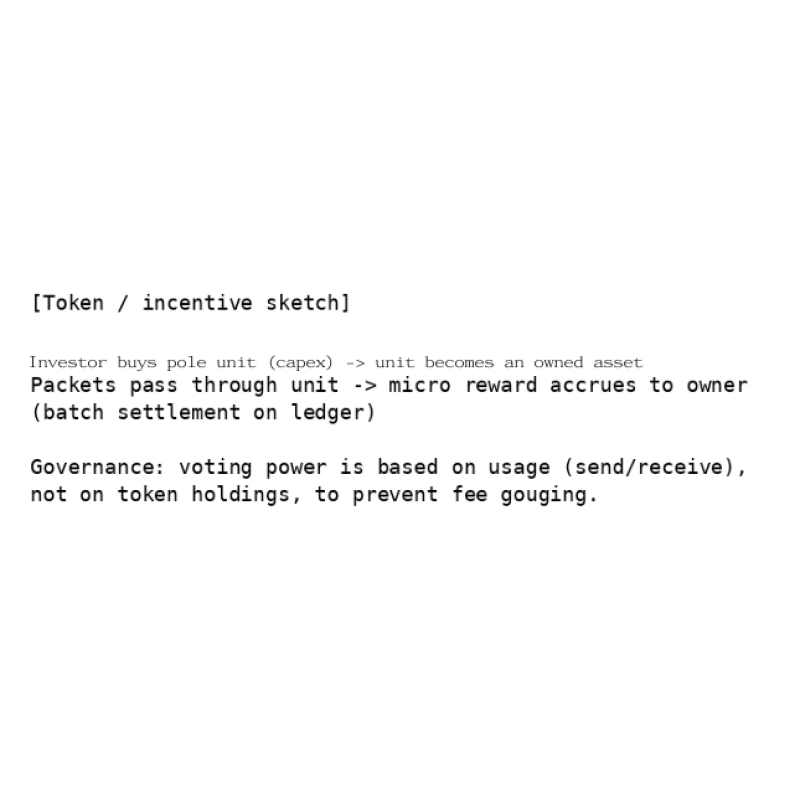
Figure 9. Concept of investment, rewards, and governance (ASCII). Pass-through rewards can be settled in batches; voting is based on usage volume. |
2026-01-12 19:31:15
| physical internet 10. Software L1/L2 (Two-Layer Architecture) |
10. Software L1/L2 (Two-Layer Architecture) Analogous to crypto L1/L2 (e.g., Ethereum L1 and an L2), the software stack is split into two layers.
The unchanging fundamentals - fixed location, map, consent, safety, and audit - are treated as L1
(immutable). New features and optimizations are implemented as L2 (upgradable). This separation
prevents L2 failures from collapsing the whole network.
L2 may be implemented by large software companies (similar to how Google dominates smartphone
ecosystems). Ideally, users can choose among L2 providers, but network effects may lead to
oligopoly or monopoly. Even in that case, the L1 constitution must prevent deviation. 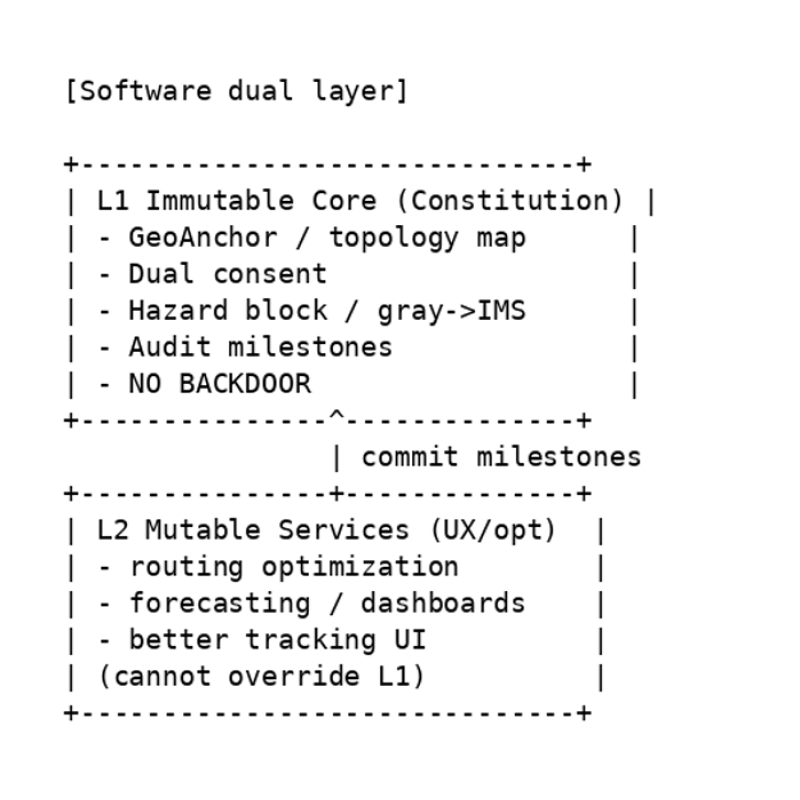 Figure 10. Immutable L1 core and upgradable L2 extensions (ASCII). L2 cannot override L1; on failure, the system falls back to L1 mode. |
2026-01-12 19:31:35
| physical internet 11. No Backdoors and Open Core |
| 11. No Backdoors and Open Core The system fixes 'no backdoors' as a safety constitution. If a privileged actor could ignore sensors or
consent via a hidden mode, severe misuse (including transporting hazardous items) would become
possible. Therefore, the core (L1) should be open source so that third parties can verify the absence
of backdoors.
At the same time, unit onboarding must be controlled so that malicious units cannot connect
arbitrarily. Joining should be guaranteed through mechanisms verifiable on the ledger, such as
certification by the integrated operator and witnessing by adjacent units
|
2026-01-12 19:32:07
| physical internet 12. Integrated Operator AI (Monitoring-as-Deterrence Concept) |
| 12. Integrated Operator AI (Monitoring-as-Deterrence Concept) In practice, a consolidated operator company will likely run the network, but human operators may be
influenced by incentives and desires. This proposal introduces the concept of an 'integrated operator
AI'. The idea is to embed the assumption that 'unit AIs are watching the whole system' as a deterrent
against deviation (backdoorization), without fixing the detailed deliberation algorithms today.
Because the evolution of AI is uncertain, the concrete content of monitoring and deliberation is left to
the future. However, the reference basis must remain consistent with the public audit logs defined in
L1.
|
2026-01-12 19:32:30
| physical internet 13. Customs Gate (National Sovereignty Domain) |
| 13. Customs Gate (National Sovereignty Domain) Whether cross-border routing is needed depends on region and era; ships and air routes will not
disappear. Therefore, customs functions should not be distributed across many IMS sites. Instead,
they should be installed as a small number of 'Customs Gate Units (CGU)', similar to airport customs.
Installation, operating rules, and interconnection conditions are decisions within national sovereignty;
the integrated operator participates only through negotiation.
|
2026-01-12 19:33:06
| physical internet 14. Constraints and Future Work |
| 14. Constraints and Future Work This document is a conceptual design; implementation requires substantial engineering and
institutional work. Open issues include: the drop-off model excludes fragile items; optimization of
home-unit sensors and cameras; optimal placement of IMS sites; standardization of power,
communications, and maintenance; and social acceptance (regulation, insurance, and liability
boundaries).
Tokenomics questions include: designing an initial capped supply and a post-cap issuance policy;
resistance to abuse in usage-based voting; and transparent reporting methods for minimum
maintenance costs. Staged expansion outlook (from household convenience to backbone) In an initial stage, the key benefit is enabling immediate shipments to and from manufacturers,
warehouses, and individuals while staying at home. Due to the drop-off model and other constraints,
items may be limited to small, non-fragile goods.
Once this convenience is experienced, the network could expand beyond utility poles into a larger
backbone network, potentially using linear-motor technology to handle fragile goods - and eventually
even human transport. If people could travel as 'packets', the travel experience itself could become an
attraction. In an era that may include epidemics, single- or two-person pods that go door-to-door
without unnecessary transfers could reduce contact and friction.
For seniors, such a system could preserve mobility even after a driver's license expires. Optimizing
logistics may also reduce traffic accidents and create broader social benefits.
For that future, the author hopes the project can start small - with ordinary electromagnetic coils and
metal spheres - and expand step by step.
|
2026-01-12 19:33:28
| physical internet 15. Conclusion |
| 15. Conclusion Speed resides not in vehicles, but in roads. Delivery speed likewise resides in the design and
operation of delivery infrastructure (a physical network). This document proposed a small-parcel
delivery system using a utility-pole unit network as a 'Physical Internet' built on a safety constitution:
consent required, hazard blocking, congestion avoidance, transparent economic design, and no
backdoors
|
 physical internet
physical internet